Sep 24, 2022
New Invention Triggers One of Quantum Mechanics’ Strangest and Most Useful Phenomena
Posted by Paul Battista in categories: computing, encryption, nanotechnology, quantum physics
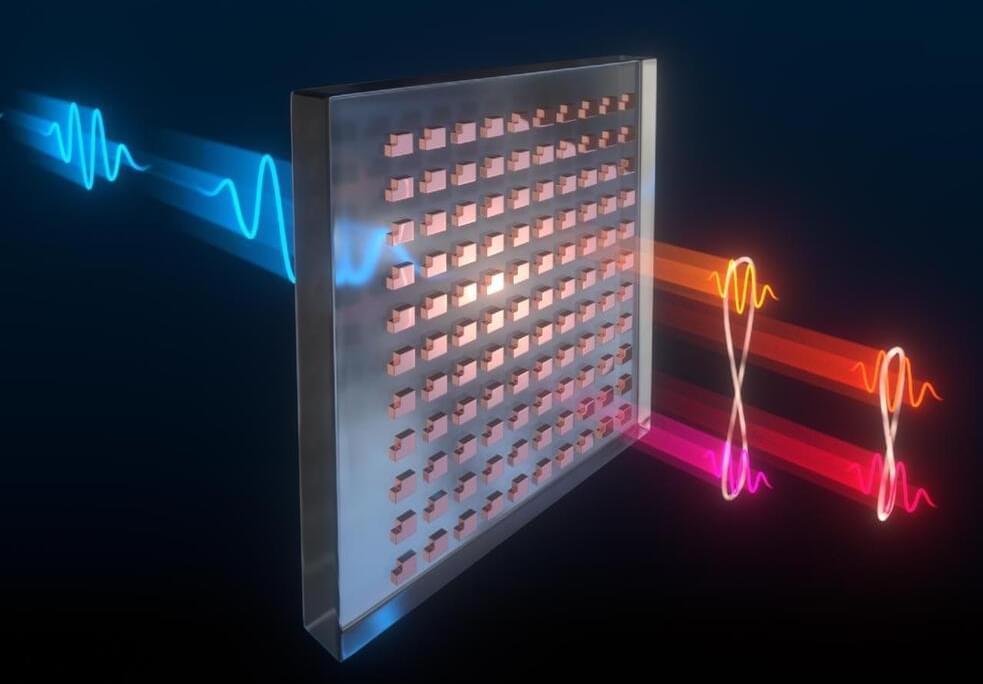
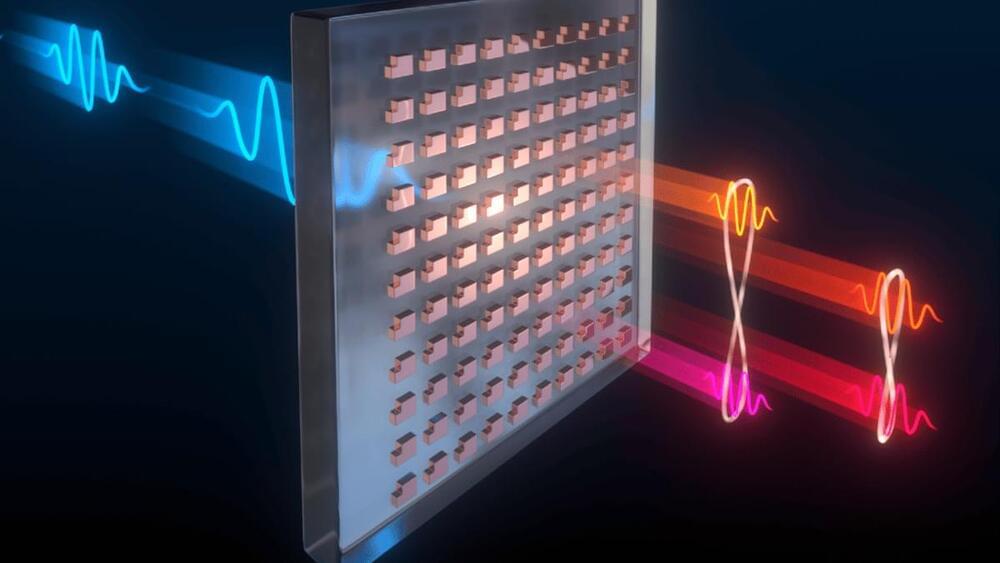
By helping scientists control a strange but useful phenomenon of quantum mechanics, an ultrathin invention could make future computing, sensing, and encryption technologies remarkably smaller and more powerful. The device is described in new research that was recently published in the journal Science.
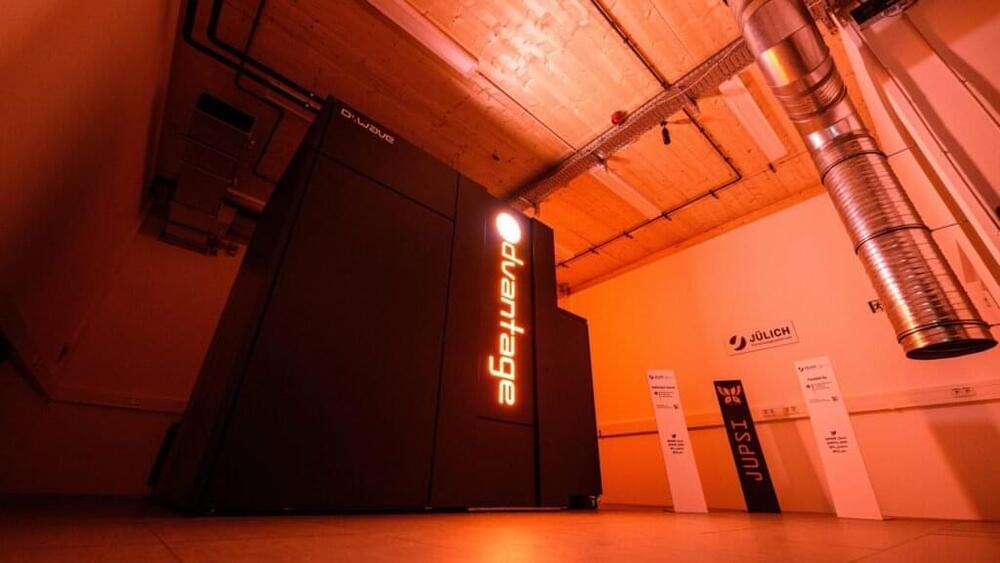
This device could replace a roomful of equipment to link photons in a bizarre quantum effect called entanglement, according to scientists at Sandia National Laboratories and the Max Planck Institute for the Science of Light. It is a kind of nano-engineered material called a metasurface and paves the way for entangling photons in complex ways that have not been possible with compact technologies.
When photons are said to be entangled, it means they are linked in such a way that actions on one affect the other, no matter where or how far apart the photons are in the universe. It is a spooky effect of quantum mechanics, the laws of physics that govern particles and other very tiny things.





 עברית (Hebrew)
עברית (Hebrew)









