Mar 7, 2021
Nanoprinted high-neuron-density optical linear perceptrons perform near-infrared inference on a CMOS chip
Posted by Genevieve Klien in categories: mobile phones, nanotechnology, robotics/AI, security
Today, machine learning permeates everyday life, with millions of users every day unlocking their phones through facial recognition or passing through AI-enabled automated security checks at airports and train stations. These tasks are possible thanks to sensors that collect optical information and feed it to a neural network in a computer.
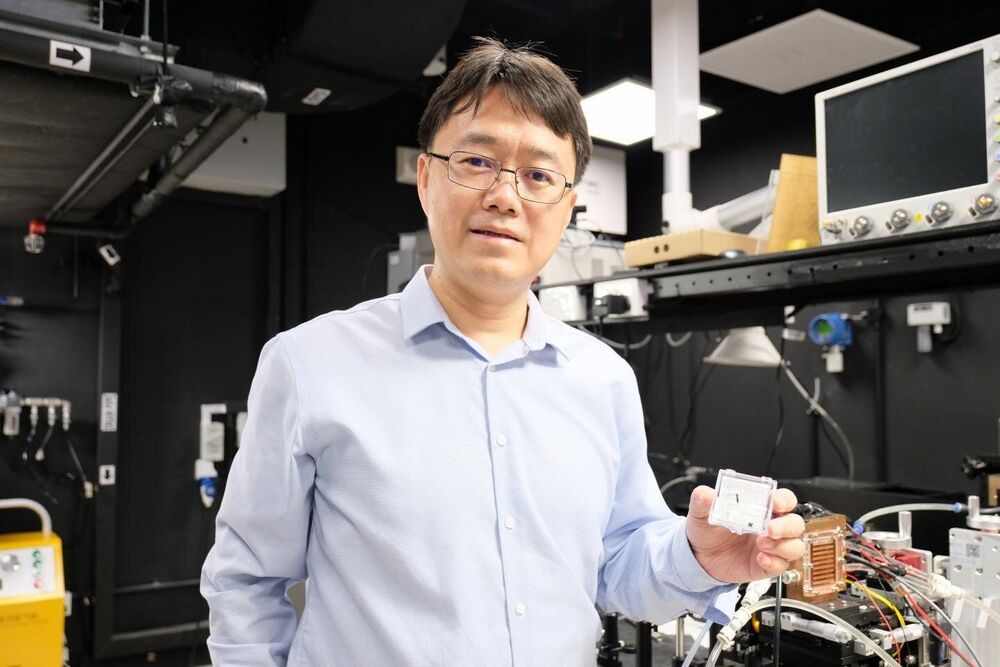
Scientists in China have presented a new nanoscale AI optical circuit trained to perform unpowered all-optical inference at the speed of light for enhanced authentication solutions. Combining smart optical devices with imaging sensors, the system performs complex functions easily, achieving a neural density equal to 1/400th that of the human brain and a computational power more than 10 orders of magnitude higher than electronic processors.
Imagine empowering the sensors in everyday devices to perform artificial intelligence functions without a computer—as simply as putting glasses on them. The integrated holographic perceptrons developed by the research team at University of Shanghai for Science and Technology led by Professor Min Gu, a foreign member of the Chinese Academy of Engineering, can make that a reality. In the future, its neural density is expected to be 10 times that of human brain.