Dec 1, 2018
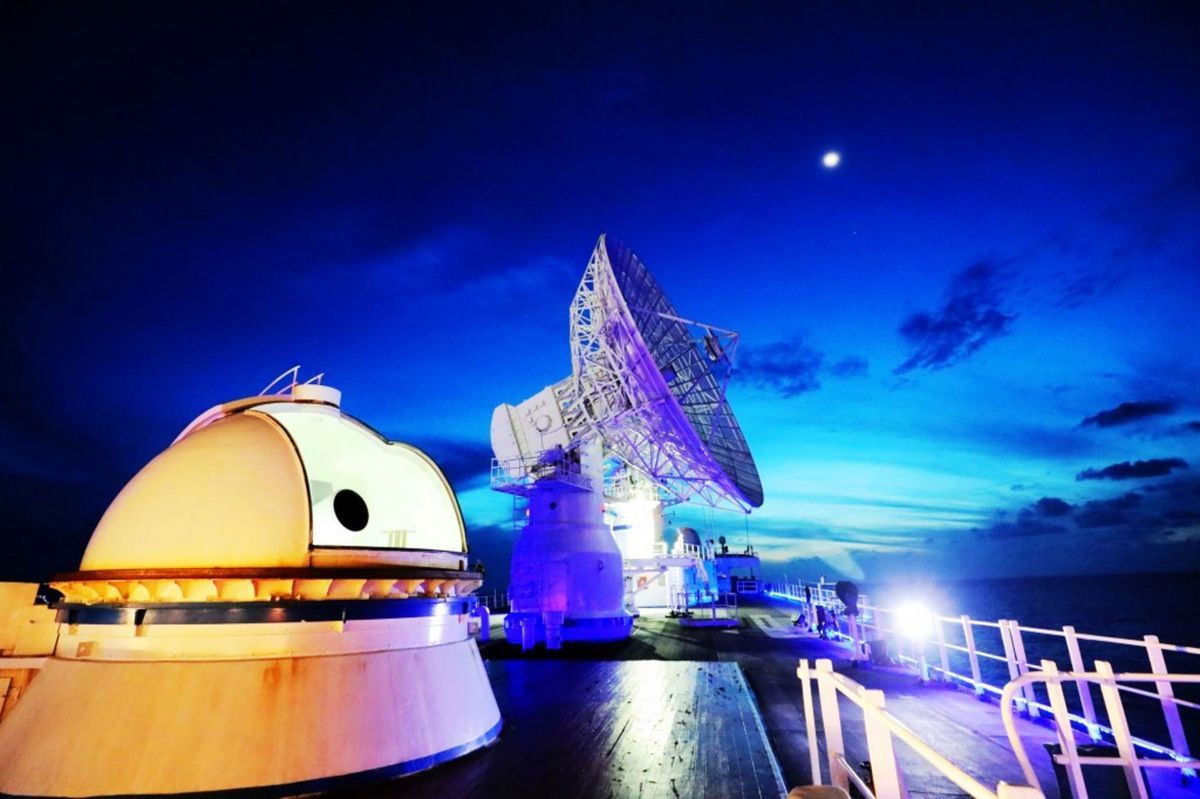
The Hidden Danger of Cleaning Up Our Space Junk
Posted by Genevieve Klien in categories: law, policy, satellites, security
As an international relations scholar who studies space law and policy, I have come to realize what most people do not fully appreciate: Dealing with space debris is as much a national security issue as it is a technical one.
Considering the debris circling the Earth as just an obstacle in the path of human missions is naive. As outer space activities are deeply rooted in the geopolitics down on Earth, the hidden challenge posed by the debris is the militarization of space technologies meant to clean it up.
To be clear, space debris poses considerable risks; however, to understand those risks, I should explain what it is and how it is formed. The term “space debris” refers to defunct human-made objects, relics left over from activities dating back to the early days of the space age. Over time that definition has expanded to include big and small things like discarded boosters, retired satellites, leftover bits and pieces from spacecraft, screwdrivers, tools, nuts and bolts, shards, lost gloves, and even flecks of paint.
Continue reading “The Hidden Danger of Cleaning Up Our Space Junk” »